In this post, we’ll explain Microsoft patches and discuss the importance of security patch management for businesses.
On the first Tuesday of each month, Microsoft releases a bundle of security patches that address newly discovered common vulnerabilities and exposures (CVEs) in Windows, Office, browsers, and other Microsoft products. Microsoft catalogs all known CVEs.
According to Microsoft, servicing for store apps does not follow the monthly “Update Tuesday” cadence but is offered whenever necessary.
What is a Microsoft security patch?
A security patch is newly released code from Microsoft inserted into the existing code of an operating system, software program, database, or browser.
These products include Microsoft Windows, Microsoft Office, Microsoft SQL Server, and Edge Browser editions.
Analogous to patching a hole in a sheetrock wall with spackle rather than replacing an entire section of sheetrock, a software patch is a stop-gap measure until a new full release of the software becomes available.
The official name for an individual patch is a Security Update. Microsoft defines a Security Update as “a widely released fix for a product-specific, security-related vulnerability.”
In 2020, by August, patches had been released for a whopping 862 CVEs, more than the total for all of 2019. Not surprisingly, there’s general agreement that this increase correlates to many people working from home.
Severity levels for vulnerabilities
Microsoft has defined four levels of severity for vulnerabilities. They are:
- Low
- Moderate
- Important
- Critical
According to Microsoft, a critical vulnerability allows a cyber attacker to take control of an employee’s computer without the user having to do anything—or by a user doing something as basic as visiting a web page or opening an email.
Once an attacker takes control of a machine, they could:
- Install programs
- View, change, or delete data
- Create new accounts with full user rights
Even if there’s nothing of apparent value to an attacker on a machine, an attacker could use the machine to launch other attacks. If the attacker deems a machine powerful enough, they could use it for crypto-mining.
Only a tiny percentage of vulnerabilities are rated critical. However, like the risk of contracting a disease from an area of virus-carrying mosquitoes, it only takes one mosquito bite to get infected.
Microsoft recommends that customers apply critical updates immediately. But there’s a caveat…
When should you patch?
There are two essential questions:
1. Should all your business’s Windows machines have patches applied every month?
2. Should all patches be applied immediately after they’re released?
The respective answers are “yes” and “not necessarily.”
New patches can cause issues with existing applications, which creates additional work for your team and can result in lost productivity.
For example, a July 2020 patch caused Outlook and other programs to crash.
A commenter on this blog post noted:
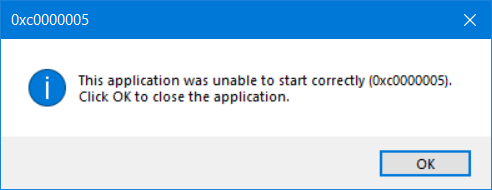
“It’s not just Outlook that’s crashing. Paint.NET, Dell’s SupportAssist, and Microsoft’s own Event Viewer also started crashing immediately on my system, with the same 0xc0000005 error code.”
One of Microsoft’s suggested workarounds before the release of a fix was to use your phone for email.
We’re investigating whether a recently deployed update could be the source of this issue. As a workaround, users can utilize Outlook on the web or their mobile clients. Additional details can be found in the admin center under EX218604 and OL218603.
— Microsoft 365 Status (@MSFT365Status) July 15, 2020
Why implement security patch management?
Security patch management provides the right balance between ongoing threat protection and installing a patch that creates more issues than it fixes (at least in the short term).
In today’s more distributed work environment, fewer people are connected behind a firewall, making ongoing patch management more important than ever.
As part of Fortis’ Defensor cyber security offering, we may delay the installation of certain patches for our customers for up to two weeks from the release date. This is so we can thoroughly test and determine how the installation impacts common business applications.
Our network operation center technicians conduct these tests to identify errors and conflicts with existing applications.
Whether your internal team is responsible for patching Microsoft products or you work with an outside, trusted advisor, we recommend implementing security patch management procedures.
“But we’ve never had an incident”
The words “past performance is not indicative of future results” are in every mutual fund prospectus or investment disclosure.
The same statement can be made about computer security. Just because none of a business’s computers have ever been known to have been compromised by an attacker doesn’t mean an incident cannot happen in the future.


