At Fortis, we take business cybersecurity very seriously and strive to keep our customers as informed as possible. Consider the following a cautionary tale.
A password manager is a tool that helps users generate and store strong, unique passwords for all of their online accounts. The master password, also known as the “key” password, is used to encrypt and decrypt the user’s password vault. It is the only password the user needs to remember.
In December 2022, password manager vendor LastPass announced a security incident. According to LastPass, 70,000 organizations use their business password management app.
Read the LastPass announcement →
The Worst Part of The Incident
As part of the LastPass breach, the bad actors copied a backup file that contained “fully-encrypted sensitive fields such as website usernames and passwords, secure notes, and form-filled data.”
From there, the attackers could use automated tools to attempt to crack each user’s account sequentially. If a user’s master password is weak, it can be cracked in minutes or days.
Everything you need to know about the breach →
After successfully cracking someone’s account, attackers would gain access to all the user’s online credentials. They could either use the credentials or sell them on the dark web.
LastPass users with weak master passwords were well-advised to change all their online passwords.
A significant takeaway from this incident is the need to ensure all your employees’ master passwords are strong.
Master Password Best Practices
Conventional wisdom is that a strong master password should be 12 or more characters long and include a mix of uppercase and lowercase letters, numbers, and special characters.
LastPass provides an example 18-character master password on its website. Here is an analysis of their example using one of many online password checkers.
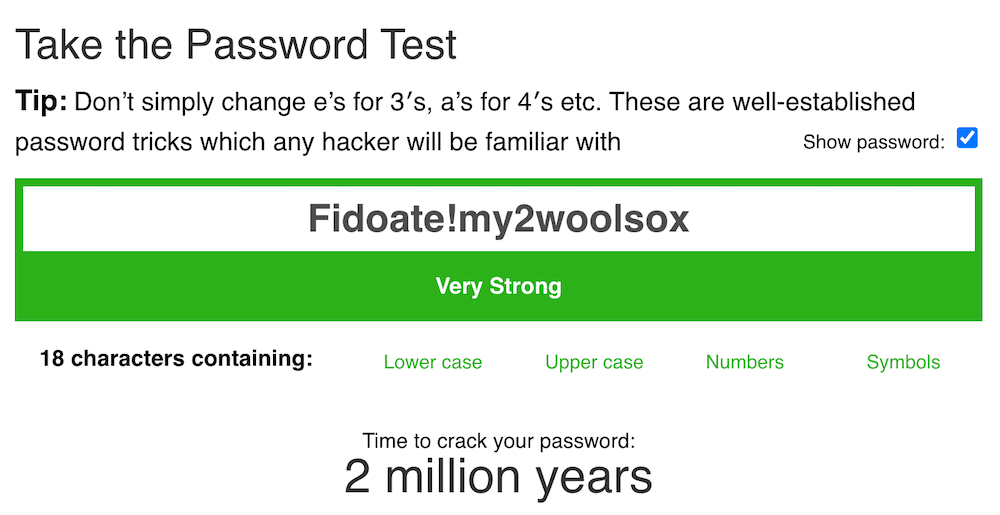
This form of a master password has a long crack time and is relatively easy to memorize.
Converting the LastPass example to a six-word passphrase results in a longer crack time and an easier-to-remember password.
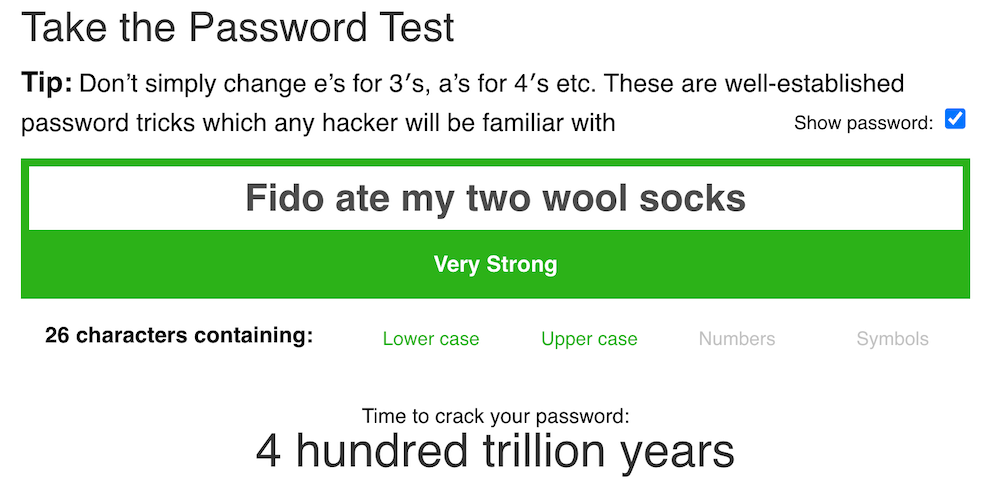
Take your pick. Either way, it’s essential to convey this master password construct to employees, so they don’t create master passwords that are easy to crack.
Users should also be instructed to avoid using personal information such as their name, location, or birthdate in their master password, as attackers may be able to obtain this information through social engineering or online research.
No matter what password manager your business uses — LastPass, Keeper, 1Password, or another brand — strong master passwords will better protect your employees from any type of incident.


