The accounting industry continues to be transformed by changing technology, where staff members work from, and an increasing number of outsider threats.
With an eye-watering number of challenges and changes and with increasingly sophisticated threat actors, the industry needs to be more vigilant than ever about ensuring the security of sensitive client data.
California CPA firms are subject to various regulations, standards, and guidance. The legal requirements differ depending on the specific services an accounting firm provides.
There’s no shortage of regulators and advice providers out there. Entities include:
- The IRS
- California Franchise Tax Board (and other states’ equivalents)
- California Board of Accountancy
- AICPA
- A firm’s professional insurance company
- The FTC
- The EU (for firms with clients that do business in the Eurozone)
Any accounting firm that prepares tax returns professionally is familiar with IRS Publication 4557, “Safeguarding Taxpayer Data,” and the FTC’s Safeguard Rule.
By ‘safeguarding,’ the IRS means taking many steps to prevent data from getting into the hands of people who should not have access to it. “Identity thieves” are called out as the principal villains.
Under federal law, financial institutions must comply with safeguard rules set by the FTC. The term “Financial institutions” is broad and includes professional tax preparers.
The Safeguards Rule requires implementing and maintaining a written information security plan (WISP). In August 2024, the IRS updated its extensive guidance on WISP documentation for tax & accounting practices.
There is a broad list of FTC recommendations. Some of these are operational tasks such as documentation and employee training. Others fall under the domain of proper information technology implementation and maintenance.
There is also the 46-page IRS Publication 1345, “Handbook for Authorized IRS e-file Providers of Individual Income Tax Returns.”
All tax preparers know the Data Security Responsibilities section of IRS form W-12.
“I am aware that paid tax return preparers must have a data security plan to provide data and system security protections for all taxpayer information.”
While many regulations & recommendations are specific to taxpayer information, accounting firms would do well to comply with the same set of standards for other services that involve managing sensitive client data.
Summary of Key Safeguards for Accounting Firms
We have assembled a collection of several specific steps accounting firms must or should take to secure client data. This is not an exhaustive list. Depending on the nature of your firm’s services, some may not be a legal requirement—simply good business practices.
We discuss some of the IRS and FTC guidance areas in greater detail. In some cases, we point to standard approaches to safeguarding data. We also reference solutions from specific suppliers.
Small to mid-sized accounting firms often rely on outside IT service providers (MSPs) for help with compliance and best practices. Third-party managed IT services for accounting firms are available in most U.S. markets.
Accounting firms that use outside MSPs should select providers with experience working with accounting firms and have appropriate safeguards in place.
Anti-virus and anti-malware software
Today, this software category is more commonly called ‘endpoint protection.’ It has evolved from computer anti-virus into many layers of protection across different devices, including mobile phones.
The IRS rightly cautions tax preparers to “never select ‘security software’ from a pop-up advertisement while surfing the web.”
It’s essential to pay for a well-regarded brand of endpoint protection software. Also, users should not be relied upon to update the software. That’s where remote monitoring and management (RMM) systems come into play. Part of an RMM’s job is to update software proactively.
Ensure strong employee passwords
The IRS provides some essential advice on creating strong passwords. However, Publication 4557 stops short of telling you what tools to deploy to prompt users to create strong passwords.
Requiring firm-wide use of password management software is the best way to ensure that employees create strong passwords and that they create different passwords for each online account.
Use multi-factor authentication
Multi-factor authentication helps to prevent data loss and unauthorized access to software applications.
Traditional two-factor authentication channels—email and text—have vulnerabilities. Mobile authenticator apps and hardware keys provide a higher level of security.
Solutions such as Duo MFA from Cisco help with company-wide adoption of multi-factor authentication.
Use firewalls
A firewall creates a barrier between your internal network and incoming traffic from the outside world. The goal is to block malicious traffic, such as viruses and malware.
The firewall is a hardware device that monitors incoming and outgoing network traffic. Based on security rules, it either allows or blocks data packets.
As part of the hybrid workforce, there are now two levels of firewalls to implement and maintain properly — office and home firewalls. Small business firewall appliances such as Meraki from Cisco have advanced security options that include:
- Firewall rules based on geographic location
- Content filtering
- Intrusion detection & prevention
- Advanced malware protection
Vendors like Ubiquiti and Mikrotik sell home firewalls with advanced features.
Monitor your network
Another FTC requirement is network monitoring. The term “network monitoring” is mainly used in the industry to monitor the performance of different devices on a network.
On the other hand, an Intrusion Prevention System (IDS) is more specific to monitoring network traffic for malicious network activity and then alerting an administrator or user. An example is Cisco’s open-source project, Snort.
Encrypt local computer data
Microsoft states, “Encryption helps protect the data on your device so it can only be accessed by authorized people.”
BitLocker drive encryption works with Windows 10 or 11 Pro. BitLocker will be enabled by default in Windows 11 version 24H2.
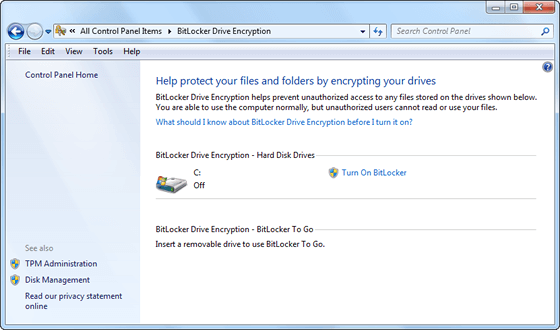
Mac users (yes, there are a few in the accounting firm world) can enable FileVault to protect local client files.
An emerging data security category provides network-wide, automatic encryption of sensitive data.
Back up and archive client financial data
CPA firms need a multi-level backup plan, including offsite backups.
The FTC safeguard rules state, “Maintain secure backup records and keep archived data secure by storing it off-line and in a physically secure area.”
Cloud backup vendors like Datto allow for fast recovery of deleted or crypto-locked client files, complete system images, and client database backups.
You can also back up your cloud files beyond the standard redundancy that cloud vendors provide.
Cloud accounting providers have backup and disaster recovery (BDR) plans.
Physically destroy old hard drives
It’s not enough to reformat a drive containing client data and then take it to electronics recycling. Drives need to be wiped entirely and physically destroyed.
The National Insititute of Standards and Technology (NIST) provides a document on media sanitation.
Hard drive destruction services exist, such as Shred-it, now part of Waste Management. Shred-it has several California locations.
Your MSP may be able to help you with physical drive destruction.
Receive client personal and financial data securely
Taxpayers sometimes send financial and personal information to their tax preparer insecurely—as plain text emails with unencrypted attachments.
While tax preparers are not technically responsible for securing client information until they receive it, the FTC guidance states, “Caution customers against transmitting sensitive data, like account numbers, via email.” Email is a risk for data leakage.
There are several ways for clients to securely share sensitive information with their accounting firm outside of email.
If an accounting firm and a client share access to a cloud drive folder on Google Drive, Dropbox, Egnyte, or Box with multi-factor authentication enabled, insecure email transmission is eliminated.
Send client financial data securely
Accounting firms must send clients documents containing confidential financial information and social security numbers.
Tools like SafeSend can be used. SafeSend gives a client secure access to information such as prepared tax returns. The email and attachments do not contain confidential information.
Obtain cyber insurance coverage
In Publication 4557, the IRS suggests that you “Check with your professional liability carrier about data theft coverage.”
Cyber liability insurance is a level of business protection that many businesses, including accounting firms, have been adopting. This is for several reasons, including the fact that some accounting firms’ business clients require cyber insurance as a condition of doing business with them.
Access the office network via a VPN
When work-at-home began in 2020, some accounting firms found themselves in a position where staff could not access office-based client/server applications such as Lacerte. They were also unable to access files stored on network machines.
The IRS states, “A secure Virtual Private Network (VPN) should be minimum standards for remote access to the firm’s office network.”
With today’s hybrid workforce (people working from home and the office), staff need VPN access to office-based and cloud-based client/server applications.
Migrate apps to the cloud
As a VPN alternative, some CPA firms are moving to an ‘all-cloud ‘ model because of the FTC safeguard rules and today’s distributed workforce.
A hybrid public/private cloud model makes data access more convenient for staff and eliminates the risks associated with specific client data residing on local machines.
Principals at accounting firms have much to implement to comply with federal regulations.
Smaller firms are increasingly working with a local MSP since it can be difficult for a single, in-house resource to implement and manage the technology required to support federally published safeguards.